Greetings All. A quick-ish post today, but an important one for those of us set in our ways when it comes to different technologies.
I recently found myself in need of a new, small network-switch for my home office. Like many other professionals, I work from home. Unlike many other professionals, I have worked from home (when not traveling) for the last 12+ years. My home office resembles something of a lab meets a meeting space meets a man cave, with an office in the middle of that madness somewhere. I wired the home with Cat6 upon purchasing it but I need far more than just one wall drop (I converted Cat6 phone jacks to RJ45s, I love when contractors over-build!). To that end, I have a switch in my office that uplinks to the core/server switches in my network room. I need power over ethernet (PoE) as I have multiple IP phones and video units in various states of configuration as well as a Unifi AP installed that uses in-line power. I also need layer 2 capabilities and either LLDP-MED or CDP for my phones. On the flip-side I need a quiet switch as I am on the phone (or headset) multiple hours of the day dealing with customers that hold me to higher standards than they hold themselves.
In the past I’ve used, almost exclusively, Cisco switches as I work with the brand often in my professional endeavors and find them to be easy to deploy and understand (for the most part). The switch that I am replacing in this narrative is, in fact, a Cisco 3560CX-8PS. This flavor of 3560 is fan-less (quiet) and provides 8 Gigabit Ethernet ports with PoE+ (15.4 watts). It also has two copper/SFP Gigabit uplink ports as well. Additionally it supports basic inter-VLAN routing, which is not terribly important given the satellite nature of where it is deployed (VTP from the core). While this switch is great, it is bigger (physically) than it needs to be and it cost me around $800 on the gray market. Additionally, I found that I needed it for another project and thus I began searching for an office replacement. I first started my search by looking for another 3560CX, I can find refurbished models for $500-1000. I like Cisco gear, but not for that price. I looked at some HPE/Aruba options but those too are more expensive than I’d like and have roughly the same size constraints as mentioned above.
At this point I started to question what I really needed. I need the ability to tag and trunk VLANS and perform the other basic tenants of a solid Layer 2 switch. I need either Cisco Discovery Protocol (CDP) or Link Layer Discovery Protocol – Media (LLDP-MED) for my phones and video units. I need PoE, as stated before, but I honestly don’t need 8 ports, I could do with 4 in most situations. I want something small and I need something quiet. To that I end I looked where I should have started looking in the first place…Ubiquiti.
If you’ve read any of my other blog posts, you know that I have Ubiquiti wireless APs and that I also have a Ubiquiti USG security gateway, I’ll put a link here if you are curious about that adventure. With the APs and USG I have a Unifi Network Controller that is constantly running and provides very useful insights on the wireless and security portions of my network. With all of that said, their switching offerings were my next logical step and I went on Amazon and found a US-8-60W switch for $125 with tax (and free shipping). If you know Ubiquiti models, you will figure out that this is a previous generation of the controller-based 8-port PoE (on 4 ports) Gigabit Layer 2 switch. It is fan-less (quiet!) and has an external power supply that can be easily hidden. The 4 PoE+ ports supply up to 15.4 watts of power per interface and it has native support for LLDP-MED.
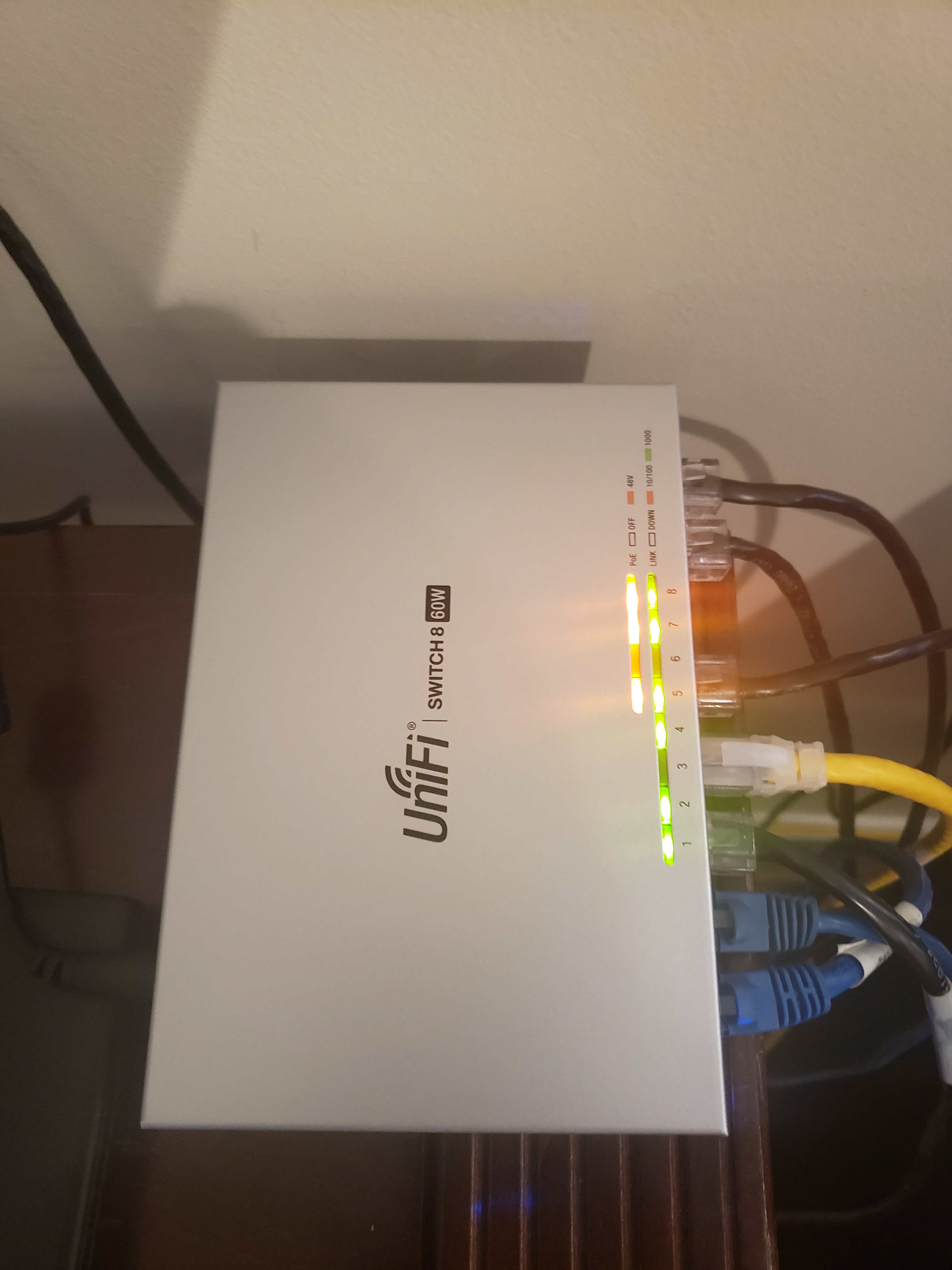
The installation was simple. I plugged it in and connected the uplink. It was adopted by the controller (with the help of Layer 2 discovery and DNS records) and the code was upgraded. From there I created port profiles and assigned them to the 8 ports.
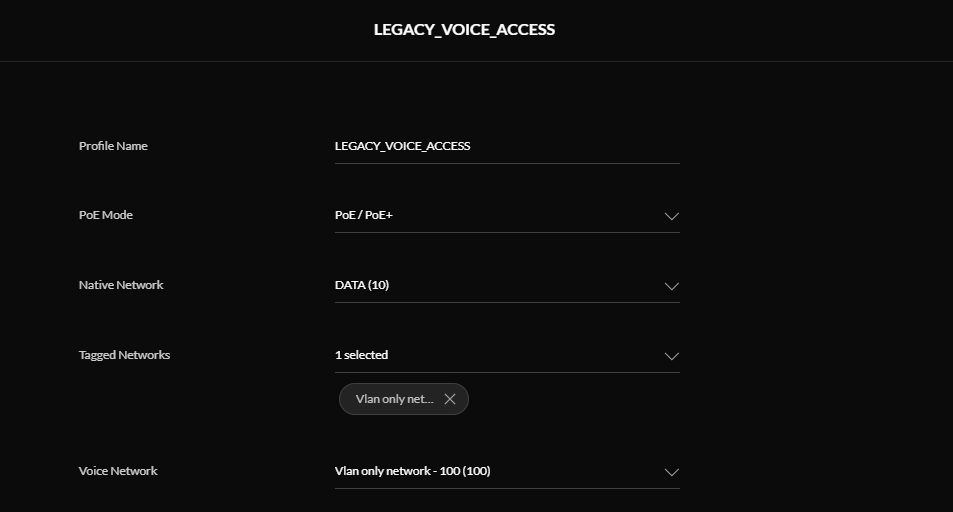
From my initial testing, I found that LLDP-MED does exactly what I need it to and the interoperability with my Cisco core/server switches is seamless.
![]()
I also found that my Cisco IP phones had plenty of power and registered without issue on the correct VLANs.

I have been incredibly impressed by this switch, and the rest of my Ubiquiti gear. I am sure there are those that will argue that comparing Ubiquiti and Cisco is far from an apples to apples comparison. I believe that argument has merit, but I prefer to respond in this way; I was able to deploy Layer 2 switching with PoE for $125. I don’t really think anything else needs to be said.
Justin